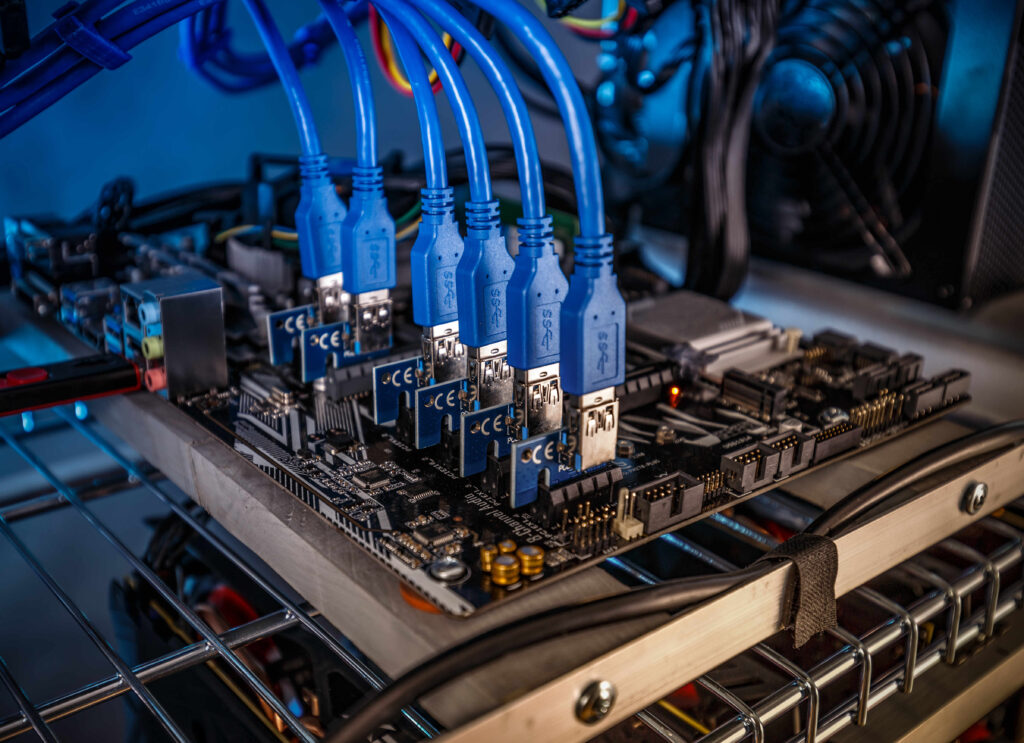
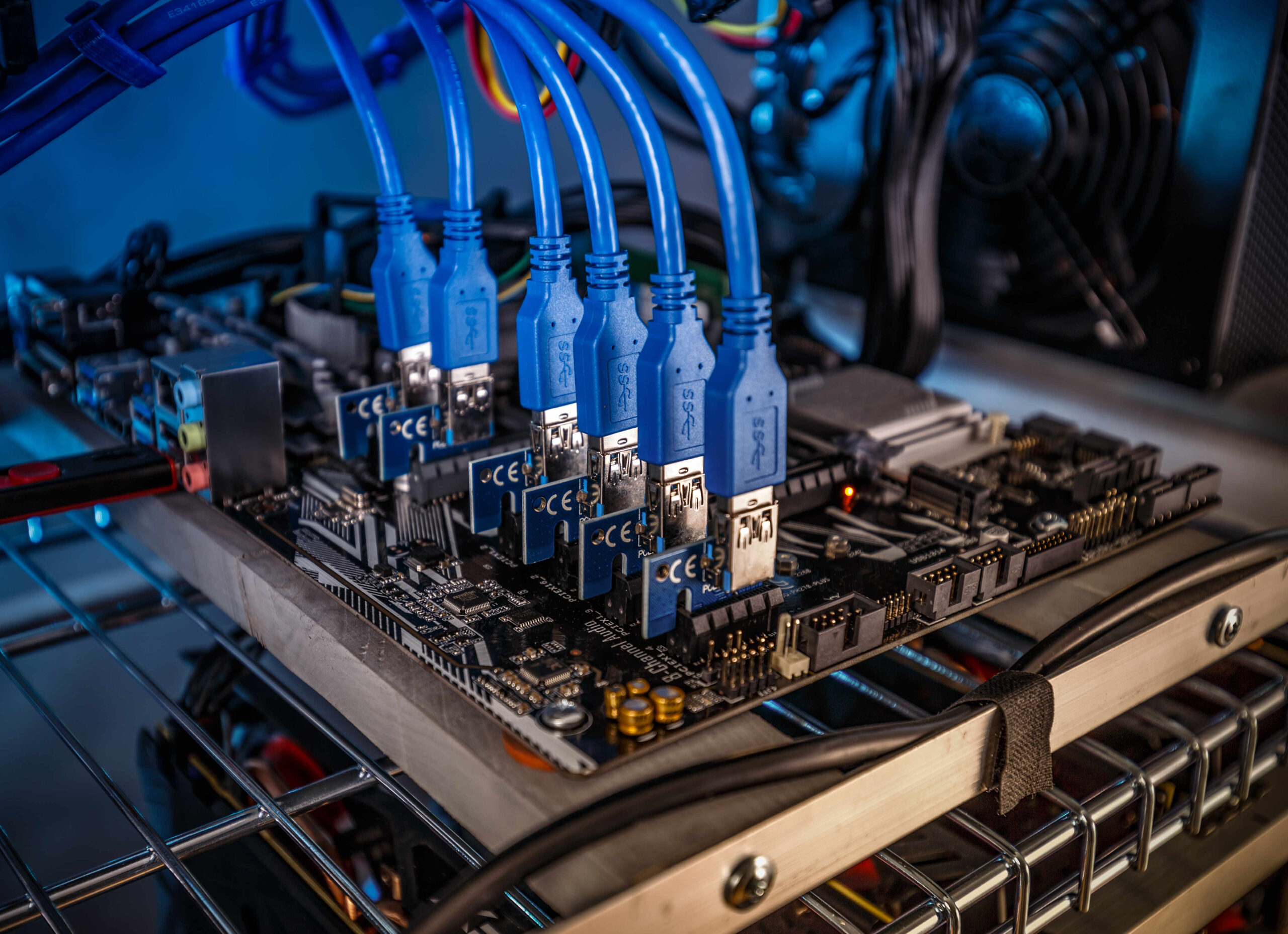
What is Hosting? Hosting a domain name means giving it a home on the internet. All …
Great Hosting, eh?
At Amray Hosting, we make web hosting simple, reliable, and built to last, just like a good old Canadian winter coat. Whether you’re setting up your first website or managing a growing business, we’ve got the speed, security, and support to keep things running smoothly. Take a look around and see how we can help get you online, hassle-free.